Highlights:
- Proof of Replication (PoRep) is a consensus mechanism demonstrating to blockchain networks that a miner can maintain and present a copy of data on a particular storage location.
- The three challenges, namely Sybil Attack, Outsourcing Attack, and Generation Attack, are all related to replication. The ability to overcome these three challenges differentiates PoRep from other kinds of proofs.
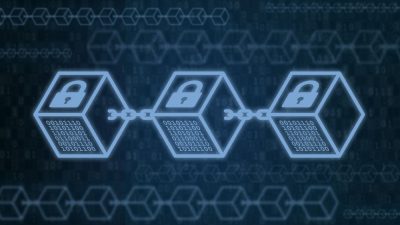
The advent of technology has touched many segments, including IT, virtualization, networking, cloud computing, storage service, cyber security, blockchain, etc. Users and businesses are flooded with various service providers in this competitive age. People demand trust, decentralized financial solutions, and transparency when it comes to blockchain. In this public network, developers, node operators, miners, and investors are active players.
A consensus mechanism is needed between these players to stay up-to-date and in consonance with the changes that keep happening. Proof-of-replication (PoRep), in short, is a process to convey that everything is going according to the regulations.
What is Proof-of-Replication (PoRep)?
Proof of Replication (PoRep) is a consensus mechanism demonstrating to blockchain networks that a miner can maintain and present a copy of data on a particular storage location. This combines proof-of-reliability (PoR) with proof-of-space (PoS), two additional mechanisms.
Users can save data on a server, verify that it is stored, and then retrieve it, thanks to proof-of-reliability (PoR). A user can outsource storage space to a network server using proof-of-space (PoS), a kind of proof-of-capacity (PoC).
Many proof-of-space (PoS) systems let users display the availability of space for junk files. Proof of Replication (PoRep), as opposed to PoS, enables the user to store significant data in such places. Additionally, it makes efficient data retrieval possible. Proof of Replication (PoRep) incorporates Proof of Reliability (PoR) into Proof of Space (PoS). The combined technique has many advantages for decentralized storage networks and cloud computing.
It includes a one-time setup of security parameters. Then pre-processing of algorithms and data inputs happens. After processing data, the replication and extraction of data are done. Then the main part comes into the picture, data that is replicating a proof. After proof replication, the PoRep verifier outputs a decision to accept or reject a proof. Verifiers and provers use this procedure.
Running a proof of replication (PoRep) is almost always more expensive than running a proof-of-space (PoS). This is because of PoRep’s ability to access these files and store both useful and junk information. Fortunately, PoRep shares characteristics with other pricing models.
PoRep operates on arbitrary data; while doing so, it follows below significant steps:
- PoRep Set Up
- PoRep Preproc
- PoRep Replicate
- PoRep Extract
- PoRep Prove
- PoRep Poll
- PoRep Verify
The rising use of cloud computing and the increasing need for decentralized storage networks compels recipients to take the help of PoRep.
Let’s Walk into the Benefits of PoRep
The PoRep is dynamic, publicly verifiable, non-outsourceable, and transparent. In addition to supporting retrievability, it is also time-bounded. Here are some of the benefits –
Effective channel: PoRep creates an effective channel for the user to have a server to keep duplicate copies of data. At the same time, it prevents users from storing the same kind of file on different servers.
Prevent outsourcing: The PoRep was created to stop a miner from delegating responsibility for certain tasks to other miners. Because proof verification verifies a prover’s identity, a miner cannot claim ownership of another miner’s work.
Transparency: PoRep provides maximum transparency as they are publicly verifiable unless the data is private or surreptitiously generated data. It allows any party to have access to data with a validating key.
User-friendly: PoRep is highly user-friendly, enabling users to extract and update the stored data without restarting the protocol. Hence, specific steps are not required to obtain data. To avoid imposters, users show and prove full PoRep in a specified time.
Protection from alien attacks: PoRep is highly effective in the cloud and decentralized storage network systems. It assures the user that stored files have a replica and is independent of the original file in a realistic manner. It creates a unified decentralized storage network where users and servers are protected from outsourcing attacks, Sybil attacks, and generation attacks.
Publicly verifiable: A PoRep includes a one-time setup run by a trusted party or a committee that runs a multi-party computation (MPC) protocol to generate the public parameters. This transparent PoRep process does not possess any private information. This is a one-time, independent setup where a trusted party that runs that particular setup will no longer be involved in the interactive protocols. It is a trusted channel for publicly verifiable data replication security.
Other Kinds of Proof Vs. Proof of Replication
The PoRep is a powerful method to operate arbitrary or random data. Other schemes like PoS and PoRet have significance but do not completely fulfill users’ expectations. So, PoRep is an extended version of all schemes to hop with the replication, deduplication, Sybil identities, and networks.
The three challenges, namely Sybil Attack, Outsourcing Attack, and Generation Attack, are all related to replication. The ability to overcome these three challenges differentiates PoRep from other kinds of proofs.
To cope with the different attacks, we can create different strategies to construct proof-of-replication protocols. Some protocols may be trusted hardware; some may be time-bound protocols. Using time-bound PoRep and relying on local time from the verifiers’ perspective, we create the most suited decentralized storage network.
While making a PoRep strategy against Sybil attack, ensure that encoding is distinguishable and incompressible. While making a PoRep strategy against outsourcing and generation attacks, it is important to make sure that the prover does not get a replica just in time. It is the time between receiving the challenge and producing the proof.
Wrapping Up
The development of blockchain is very much needed at this point in time. As the technology is widening its branches all over the way, transparent, concise, more user-friendly, and trustful decentralized solutions are needed to have more reliability to opt over traditional centralized financial solutions.